Technology alone cannot prevent cyber-attacks.
Over 90% of all successful cyber-attacks are a result of information unknowingly provided by employees.
Why Choose Us?
Our cybersecurity assessment tool is designed to provide comprehensive protection for your organization. With advanced features like threat detection, vulnerability scanning, and risk management, we ensure your systems are secure and compliant. Stay ahead of cyber threats and protect your critical assets with our cutting-edge solution.
Secure your digital future with us. Experience the peace of mind that comes from knowing your cybersecurity is in expert hands. Join us today and take the first step towards a safer digital world.
Cybersecurity Assessment
A high-level analysis of your organization’s overall security posture, examining the effectiveness of security controls and identifying potential vulnerabilities
Cybersecurity Audit
A detailed evaluation of your cybersecurity policies, procedures, and systems to ensure they align with established security standards and best practices.
Enhanced Security Posture
Gain actionable insights to improve your organization’s security posture, including implementing stronger security controls and updating policies.
Compliance and Trust
Ensure compliance with relevant laws and industry regulations, maintaining trust with stakeholders.
Proactive Threat Management
Stay ahead of potential threats by regularly conducting security audits and assessments.
Collaborative Approach
ANIKI enables holistic approach to foster a culture of security and vigilance, making your organization more resilient against cyber threats.
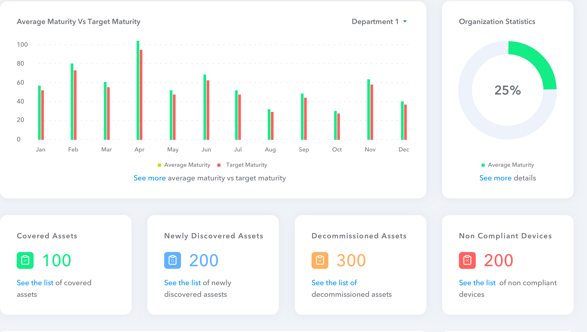
Dashboard View of Company’s Cybersecurity Status
A high-level summary of the organization’s Overall Cybersecurity status, including key metrics and indicators, number of identified vulnerabilities, their severity levels, and remediation status.
Incident Response
Keep track of recent security incidents, monitor response times, and review resolution status.
Vulnerability Assessment
Proactively identify and mitigate potential vulnerabilities before they can be exploited. Display an overview of recent security incidents, response times, and resolution status.